Step-by-Step Guide – How to Configure Your First App Protection Policy in Microsoft Intune
App Protection Policies (APP) are one of the most effective tools for protecting corporate data — especially in BYOD environments. If you’re looking to control how data is accessed and used inside business apps (like Outlook, OneDrive, or Teams), without enrolling the entire device, this is the way to do it.
This guide walks you through how to configure your first App Protection Policy in Microsoft Intune, step by step.
Before you begin, ensure:
- You have Microsoft Intune admin access
- Your licensing includes Microsoft 365 Business Premium, EMS E3/E5, or M365 E3/E5
- Your users are signing into apps using their work accounts
Step-by-Step: Creating an App Protection Policy
Step 1: Sign in to the Intune Admin Center
Go to: https://intune.microsoft.com
Step 2: Navigate to App Protection Policies
- Click on “Apps”
- Select “Protection”
- Click “+ Create policy”
Step 3: Choose Your Platform
- Select either “iOS/iPadOS” or “Android” depending on your target users

Step 4: Fill in the Basics
- Give your policy a name (e.g., “Android BYOD App Policy”)
- Optionally add a description for clarity

Step 5: Assign Targeted Apps
Select the apps you want the policy to apply to.
Recommended Microsoft apps:
- Core Microsoft Apps – It will cover all the core M365 apps as you can see on the screenshot

Step 6: Configure Data Protection Settings
These settings help control how data is accessed or shared.
Examples include:
- Prevent backup to iTunes or Google Drive
- Restrict cut/copy/paste to managed apps only
- Encrypt app data when device is locked
- Disable saving files to unapproved locations

Step 7: Configure Access Requirements
Define how users authenticate into the app:
- Require a PIN to open
- Allow biometric unlock
- Set session timeout thresholds

Step 8: Set Conditional Launch Rules
Control when the app is allowed to launch based on risk signals:
- Block access on jailbroken/rooted devices
- Require minimum OS version
- Wipe data if offline for X days
- Wipe data for disabled account

Step 9: Assign the Policy to Users/Groups and save it
- Assign the policy to a user group (not a device group)
- It’s best to start with a pilot group to test


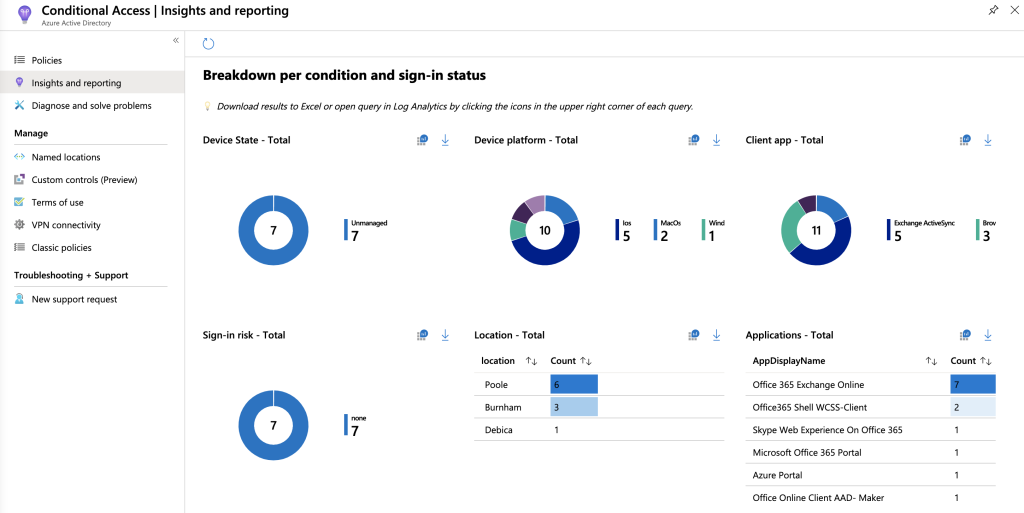
Step 10: Monitor
- Go to “Apps > Monitor > App protection status” to check deployment, enforcement, and any policy conflicts

Best Practices
- Start with a small pilot group
- Educate users before rollout
- Use consistent naming conventions
- Regularly review policy effectiveness in reporting
- Combine with Conditional Access for stronger enforcement
App Protection Policies allow you to enforce corporate data protection in apps without managing the full device. That’s a win for security and a win for user privacy — especially in hybrid or BYOD scenarios.
If you haven’t deployed your first policy yet, this is a great place to start.